Operation Triangulation: The last (hardware) mystery
Hacker News
DECEMBER 27, 2023
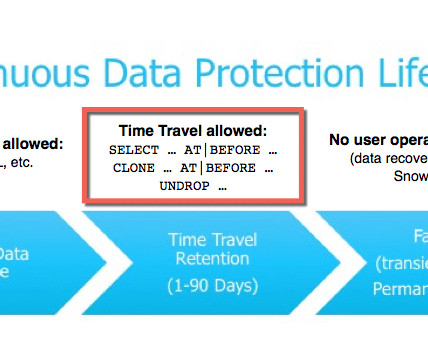
We discovered that to bypass this hardware-based security protection, the attackers used another hardware feature of Apple-designed SoCs. Technical details Various peripheral devices available in the SoC may provide special hardware registers that can be used by the CPU to operate these devices. The prompted me to try something.











Let's personalize your content