The Notebook by Roland Allen review – notes on living
Hacker News
DECEMBER 15, 2023
From plans for flying machines to philosophy – the remarkable joy of jotting things down

 jot
jot 
Hacker News
DECEMBER 15, 2023
From plans for flying machines to philosophy – the remarkable joy of jotting things down

Hacker News
JUNE 16, 2023
Maria Naumcheva, Sophie Ebersold, Alexandr Naumchev, Jean-Michel Bruel, Florian Galinier and Bertrand Meyer: Object-Oriented Requirements: a Unified Framework for Specifications, Scenarios and Tests, in JOT (Journal of Object Technology), vol. 1, pages 1:1-19, 2023. Available here with link to PDF (the journal is open-access).
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Dataconomy
JANUARY 2, 2024
Whether it’s jotting down meeting minutes, capturing important ideas, or organizing thoughts, note-taking helps businesses stay organized and productive. Note-taking has always been an essential part of business operations.

Dataconomy
AUGUST 22, 2023
From tracking progress and offering real-time feedback to enabling learners to engage with audio lectures or jot down voice notes, wearable devices like smartwatches and VR headsets are making academic pursuits both convenient and interactive.
Towards AI
APRIL 10, 2024
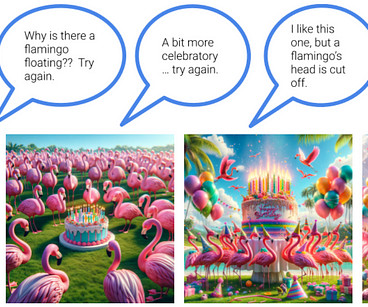
On the other extreme, if you quickly jot down “Happy Birthday” on some craft paper and then sign your name, you have technically “made” the card, but it hasn’t been made special. What if you went out of your way to Hallmark, spent an hour selecting a card, wrote a few paragraphs, and included some old photos?
Smart Data Collective
NOVEMBER 5, 2020
It would be more convenient as compared to jotting it down on a sheet of paper. These specialties work in favor of your privacy and can greatly enhance it. For example, at a hospital, all the health care prescriptions and related health care data can be stored on your card. Protected transmission.
Smart Data Collective
NOVEMBER 9, 2022
Examples of inferior cyber hygiene include not using two-factor authentication to access company accounts, jotting down passwords on sticky notes, using unprotected Wi-Fi networks, and misplacing personal devices which have been used for work. . This is also going to be a greater threat as more hackers use AI to identify weak targets.
Let's personalize your content