Understanding data breach meaning in 4 steps
Dataconomy
JANUARY 2, 2024
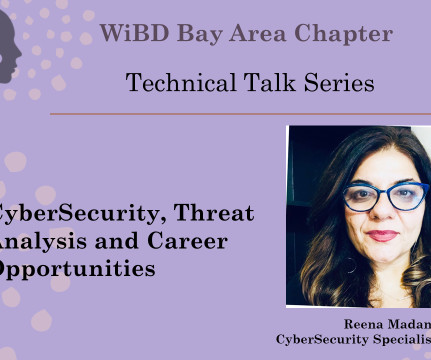
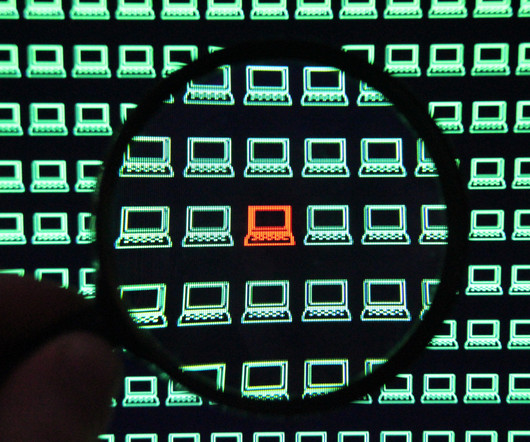
Cybercriminals or unauthorized entities exploit vulnerabilities in security systems to gain access to this data, often intending to sell it on the dark web, use it for identity theft, or hold it for ransom. Understanding these types is crucial for implementing targeted security measures and response strategies.














































Let's personalize your content