AWS Creates New Policy-Based Access Control Language Cedar
Hacker News
FEBRUARY 19, 2023
Comments (..)
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 accessibility-policy
accessibility-policy 
Hacker News
FEBRUARY 19, 2023
Comments (..)

Data Science Dojo
MARCH 6, 2024
In alignment with societal values, AI development faces challenges like ensuring data privacy and security, avoiding biases in algorithms, and maintaining accessibility and equity. Equity and Accessibility: Ensure that AI-driven tools are accessible to all, addressing disparities in resources, infrastructure, and education.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
How to Optimize the Developer Experience for Monumental Impact
Generative AI Deep Dive: Advancing from Proof of Concept to Production
Understanding User Needs and Satisfying Them
Beyond the Basics of A/B Tests: Highly Innovative Experimentation Tactics You Need to Know
Leading the Development of Profitable and Sustainable Products
AWS Machine Learning Blog
MARCH 13, 2024
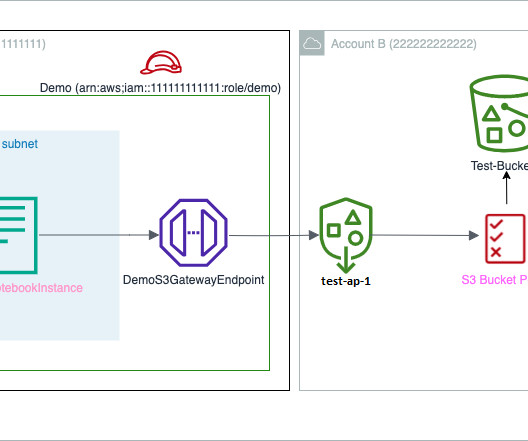
To develop models for such use cases, data scientists need access to various datasets like credit decision engines, customer transactions, risk appetite, and stress testing. Managing appropriate access control for these datasets among the data scientists working on them is crucial to meet stringent compliance and regulatory requirements.
How to Optimize the Developer Experience for Monumental Impact
Generative AI Deep Dive: Advancing from Proof of Concept to Production
Understanding User Needs and Satisfying Them
Beyond the Basics of A/B Tests: Highly Innovative Experimentation Tactics You Need to Know
Leading the Development of Profitable and Sustainable Products
IBM Data Science in Practice
MARCH 7, 2024
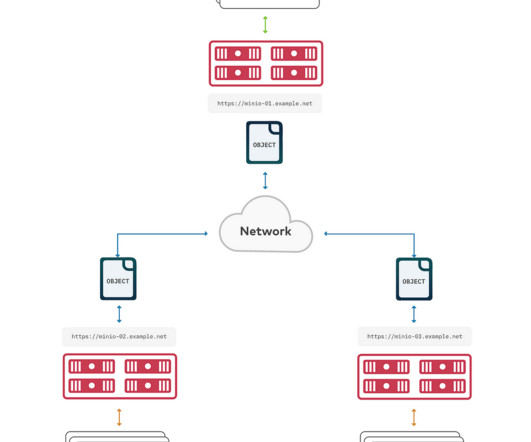
It specifies the location where the MinIO object storage can be accessed. <accesskey>: <accesskey>: The access key associated with the target MinIO object storage. This key, along with the access key, is used for authentication. This key, along with the access key, is used for authentication.

AWS Machine Learning Blog
OCTOBER 30, 2023
Amazon Bedrock is a fully managed service provided by AWS that offers developers access to foundation models (FMs) and the tools to customize them for specific applications. The API call is routed to the Amazon Bedrock VPC endpoint that is associated to the VPC endpoint policy with Allow permissions to Amazon Bedrock APIs.

Dataconomy
APRIL 17, 2024
These technologies, capable of producing complex and creative outputs, have raised questions about authorship and copyright, making Google’s updated policies a critical point of discussion in the tech community.

IBM Journey to AI blog
FEBRUARY 5, 2024
The executive order highlights the importance of securing digital assets and mitigating cyberthreats by emphasizing the modernization of identity and access management (IAM) systems. FICAM (Federal Identity, Credential, and Access Management) is an extension of ICAM protocols, methodologies, and systems for federal entities.

Data Science Dojo
MARCH 6, 2024
In alignment with societal values, AI development faces challenges like ensuring data privacy and security, avoiding biases in algorithms, and maintaining accessibility and equity. iTutorGroup agreed to pay $365,000 to resolve the lawsuit and was required to adopt new anti-discrimination policies as part of the settlement.

Data Science Dojo
JUNE 5, 2023
Access to funding, technical knowledge, and collaborations with AI experts can help overcome these barriers. Ethical guidelines and policies : Non-profits should develop clear and comprehensive ethical guidelines and policies regarding the use of AI.
ML @ CMU
JUNE 30, 2023
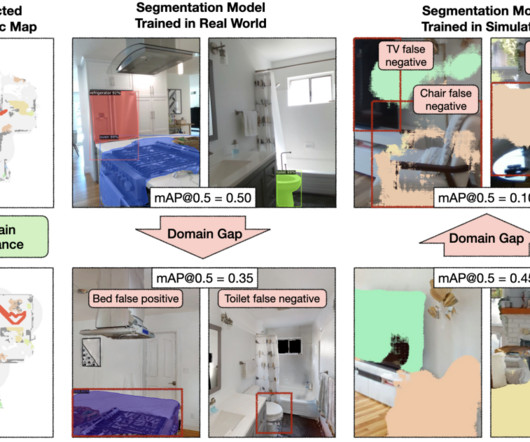
But learned visual navigation policies have predominantly been evaluated in simulation. We evaluate policies across six homes with no prior experience, maps, or instrumentation. The robot has access to only a first-person RGB and depth camera and a pose sensor (computed with LiDAR-based SLAM).

Hacker News
JANUARY 20, 2024
Firstly, we simplify the LLM decoder layer by fusing data movement and element-wise operations to reduce the memory access frequency and lower system latency. A customized Scaled-Dot-Product-Attention kernel is designed to match our fusion policy based on the segment KV cache solution.
AWS Machine Learning Blog
NOVEMBER 9, 2023
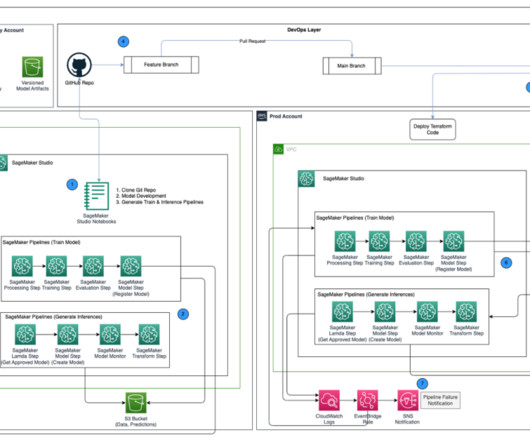
The MLOps workflow includes the following steps: Access the SageMaker Studio domain in the development account, clone the GitHub repository, go through the process of model development using the sample model provided, and generate the train and inference pipelines. Choose Create key.

Dataconomy
FEBRUARY 6, 2024
The Oversight Board of Meta has suggested that a clearly fabricated fake Joe Biden video should not be removed from Facebook, pointing out the need for Meta to revisit and potentially broaden its somewhat restrictive policy on manipulated media.

IBM Journey to AI blog
OCTOBER 24, 2023
Enterprise-managed identity and access management (IAM) enables cloud administrators to centrally configure access and security settings for the entire organization. The SRE team needs operational access to these resources for every team in every account under the company’s IBM Cloud enterprise.

The Data Administration Newsletter
SEPTEMBER 19, 2023
Through advanced technologies and tools, IT ensures that data is securely stored, backed up, and accessible to authorized personnel. IT also enforces data governance policies and procedures, such as data classification and access […]

Hacker News
APRIL 5, 2023
Because AWS IAM is eventually consistent the malicious actor was able to perform various API calls even after the AWSCompromisedKeyQuarantineV2 policy has been added. Policy attached by AWS The AWSCompromisedKeyQuarantineV2 is attached to the IAM user test-user. This policy denies the most important actions.

Hacker News
MARCH 24, 2023
If a website or other resource is hosted on IPFS, it remains accessible as long as the computer of one user who “pinned” it remains online. Most notably, Cloudflare gave it a boost by launching its own IPFS gateway , allowing the public to access IPFS resources without having to install specialized software.

Hacker News
JUNE 28, 2023
Graph-based or policy-as-code? Explore access control systems in this comparative analysis. Discover pros, cons, and a hybrid solution.

Smart Data Collective
SEPTEMBER 19, 2023
Although this information is unclassified, unauthorized access can have extreme economic and national security implications. It ensures that the personnel within these organizations get educated on the policies that revolve around information security, procedures, and best practices.

Dataconomy
FEBRUARY 7, 2024
The Ivanti vulnerability 2024, identified as CVE-2024-21893 and affecting Ivanti Connect Secure and Ivanti Policy Secure, is currently facing widespread exploitation by numerous adversaries due to a server-side request forgery (SSRF) flaw.
MAY 15, 2023
As such, here are three examples of use cases I’ve heard from fellow students—and how higher education can do a better job of incorporating the student perspective into these policies. UCLA’s new policy describes using AI chatbots as “receiving assistance from another person.”

Dataconomy
APRIL 8, 2024
He reminded that Google’s robots.txt files and Terms of Service clearly forbid the unauthorized collection or download of YouTube materials, reaffirming the company’s usage policies.

ODSC - Open Data Science
MARCH 15, 2023
Meanwhile, data security safeguards digital information and data from malicious or unauthorized access. Data security becomes paramount in a hybrid workplace since remote workers need secure access to sensitive information outside the office premises.

IBM Journey to AI blog
SEPTEMBER 29, 2023
In our blog post on identifying inactive identities , we looked at the APIs offered by IBM Cloud Identity and Access Management (IAM) and how to utilize them to obtain details on IAM identities and API keys. Recap: Inactive identities IBM Cloud Identity and Access Management (IAM) supports different forms of identities.

IBM Journey to AI blog
APRIL 24, 2024
Only administrators can access customer data on the backend. Mitigating privacy risks: The app limits data access to trusted employees who need it for their roles, and employees can access data only when they have a legitimate reason to. Retention policies should also be limited.

Smart Data Collective
MAY 17, 2023
With that said the tips in our guide will enhance the security of your Office 365 environment and minimize the risk of data breaches or unauthorized access. These policies will alert users whenever sending confidential or sensitive data through email or other communication channels.

Smart Data Collective
APRIL 30, 2022
Cybersecurity policies have become one of the top priorities for organizations, especially as the nature, frequency, and sophistication of cybersecurity attacks are rapidly evolving and the number of data breaches escalates each year. Data security must be ensured by an organization’s security policies.

Data Science Connect
JULY 22, 2023
Developing Robust Cybersecurity Policies To ensure data privacy and confidentiality, businesses need well-defined cybersecurity policies and procedures. Online security consultants assist in creating and implementing these policies, guiding enterprises in establishing secure data handling protocols and access controls.
Dataconomy
JULY 21, 2023
It is believed that the feature, which was previously only accessible to Plus subscribers, will soon be made available to all users. OpenAI claims that while Plus plan customers can access the function, people who live in the EU or the UK cannot. Access Settings. Access Settings. It’s a beta function right now.

Dataconomy
DECEMBER 21, 2023
Meta cited policy violations but didn’t elaborate further. Providing fake data aligns with the theory that Instagram Wrap lacked access to Instagram’s core data, something third-party apps can’t access just by linking with your Meta login.

Dataconomy
OCTOBER 26, 2023
This article will delve into what AI dubbing is, its growing popularity, and the top AI dubbing tools that simplify content creation and enhance accessibility. This process, known as Automated Dubbing or Video Translation, enables content to be more widely accessible in various languages. The benefits of AI dubbing are impressive.

Dataconomy
AUGUST 8, 2023
The technology facilitates data to dictate the required operating system and applications for access, ensuring that the right entities interact in a secure manner. The Trusted Computing Base (TCB) operates as the foundation for a secure system, ensuring that critical security policies are implemented and maintained.
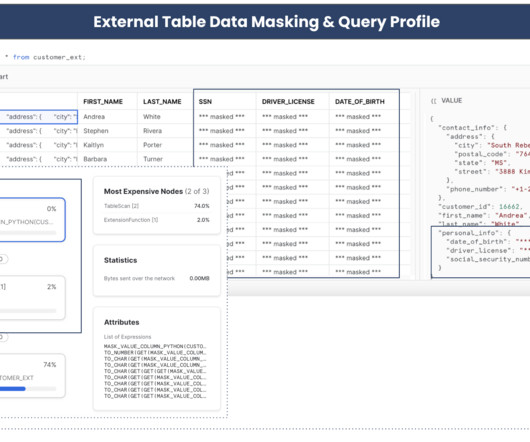
phData
OCTOBER 23, 2023
And if you want to apply a masking policy to a variant column, it’s a bit more complicated, especially with nested JSON data. Method-1: Query Named Stage Directly -- accessing staged JSON data directly using $ notation select t.$1:customer_id::number, DDL statement. You have to do it later with an ALTER command.

IBM Journey to AI blog
MAY 8, 2024
The use of various identity tools is further compounded with managing access to your legacy application infrastructure, integrating new users during mergers and acquisitions. Identity orchestration Identity and access management projects are complex enough with many taking 12-18 months.

NOVEMBER 3, 2023
My students are working toward a master’s degree in public affairs and many of them are interested in pursuing careers in international and domestic public policy. Throughout the course, students are tasked with crafting four memos on designated policy issues. My goal was twofold. Courtesy of Wendy Castillo.

Dataconomy
APRIL 22, 2024
Retention of reviewed conversations Conversations reviewed by humans are stored separately and do not link back to your Google Account, remaining accessible for up to three years, unlike the standard 30-day retention policy. Should this policy change, Google will clearly inform you of any updates.

Dataconomy
SEPTEMBER 22, 2023
This essential practice involves the transfer of data from active storage systems, where it is frequently accessed and used, to secondary storage systems specifically designed for extended preservation and infrequent access. But why do businesses need it exactly? But this data sometimes needs to be archived. Let us explain.

Dataconomy
MARCH 8, 2024
Apple, famous for its tightly controlled App Store experience on iOS and iPadOS devices, recently implemented a series of last-minute policy changes that have generated a wave of mixed reactions from the developer community. Instead, users will need a direct link from the developer in order to access and install the app.

Smart Data Collective
APRIL 20, 2022
What’s more, due to remote work, more companies use cloud technology and online networks that are easier to access remotely. What is a Secure Web Gateway , how can it prevent data loss, and how does it ensure that the data you have is used according to compliance policies? . In the past year, almost 45% of the companies in the U.S.

Towards AI
APRIL 21, 2024
However, bringing them into professional settings faces challenges because they need internet access, and some company policies simply do not allow them. As AI tools become increasingly popular, they play an important role in boosting our productivity in everyday tasks.
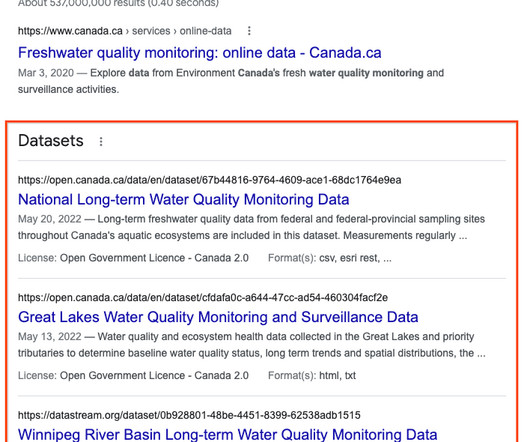
Google Research AI blog
FEBRUARY 28, 2023
Posted by Natasha Noy, Research Scientist, and Omar Benjelloun, Software Engineer, Google Research Access to datasets is critical to many of today's endeavors across verticals and industries, whether scientific research, business analysis, or public policy.
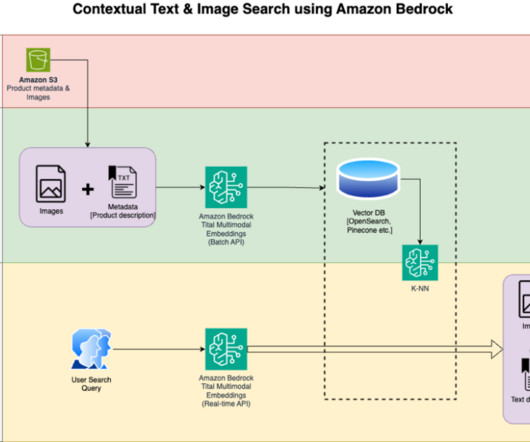
AWS Machine Learning Blog
APRIL 3, 2024
By default, the model generates vectors (embeddings) of 1,024 dimensions, and is accessed via Amazon Bedrock. You can confirm it’s enabled on the Model access page of the Amazon Bedrock console. If Amazon Titan Multimodal Embeddings is enabled, the access status will show as Access granted , as shown in the following screenshot.
phData
APRIL 19, 2024
Built in logging and metadata Fivetran logs and audit tables available in Snowflake for analysis and reporting Prerequisites Access and Permissions Snowflake Destination If this is the first time using Snowflake as a Fivetran destination, there are some steps to take as described below. Otherwise, this section can be skipped.

Dataconomy
MAY 18, 2023
Although this grants enhanced accessibility of the infrastructure for employees and customers, it also amplifies the susceptibility for malicious actors to illicitly penetrate an organization’s cloud-based resources. Second, apply strong access controls and authentication mechanisms to secure API endpoints.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content